FIND THE RIGHT GRC SOLUTION FOR YOU
The Xactium GRC product suite is now part of Riskonnect’s Integrated Risk Management platform. Click below on the Xactium GRC system that most interests you, and we will navigate you to the right place for more information.
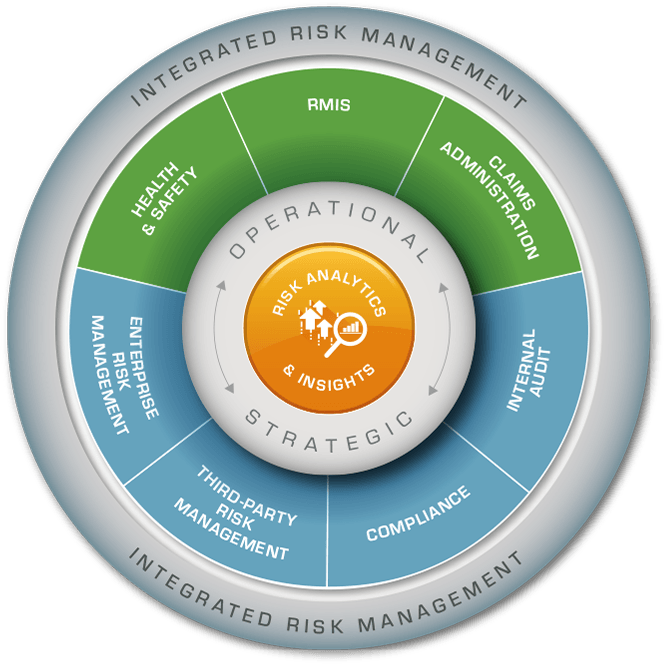
Riskonnect Integrated Risk Management
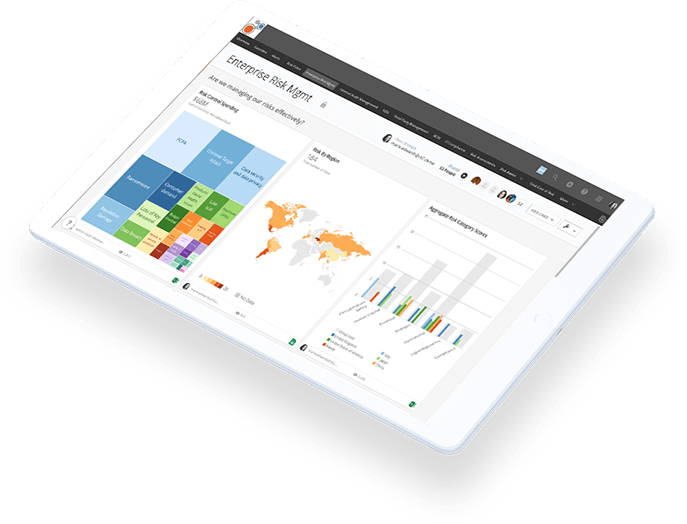
View Risk Like Never Before
Riskonnect is a global leader in integrated risk management technology and the world’s largest RMIS provider. Our Integrated Risk Management solution transforms the way you perceive and manage risk by integrating data, connecting risks, and correlating their relationships for a clear view of how risk impacts the entire enterprise.
Watch this brief video to learn how IRM makes risk and compliance management easier, faster and more effective.
HOW’S THE VIEW?
Our customers say it best.
How’s Your View?
Find out how
Riskonnect can transform
the way you view risk.